An Introduction to Ransomware
In today’s blog, we will do a quick introduction to Ransomware. Ransomware is a form of malware (short for malicious software) designed to deny access to the data on a user’s computer until a ransom is paid. Typically, ransomware is spread via phishing emails, users unknowingly visiting/interacting with an infected website, or weak passwords allowing an attacker to place the malware on an internal system.
Ransomware attacks are becoming more and more prevalent. In fact, “85% of MSPs Report Ransomware as a Common Threat to SMBs. Results from a survey in the same Datto report also indicates that 85% of managed service providers report ransomware attacks as the most common malware threat to small to mid-size businesses (SMBs).” [1]
Although ransomware attacks have been reported as far back as 1989 [2], it’s only in the last decade that the ransomware landscape has really exploded into life. Many people speculate that this is due to the rise of Bitcoin, and cryptocurrencies in general, thus making it easier for attackers to illicit money from their victims. There are many reasons why criminals use crytpocurrencies in conjunction with ransomware, two of the more obvious reasons are the perceived anonymity, and encryption. Another reason, as Peter Van Valkenburgh from CoinCenter states, is the efficiency of the Bitcoin network. [3] “The efficiency of the network is what criminals are really using it for here. It’s electronic cash, so it’s easy to write software that can automatically demand payment and automatically determine that payment has been made.” Bitcoin is by far the most widely used cryptocurrency at the time of this writing, and the most widely demanded form of ransom among the most popular ransomware variants seen in the wild. However, some ransomware groups [4] are actually switching from Bitcoin to Monero to better protect their identities. Monero is one of the most popular ‘privacy’ cryptocurrencies, as it is argued that Monero is truly anonymous whereas Bitcoin is merely pseudo-anonymous. This blog, however, will not delve into the different nuances of the various cryptocurrency ‘coins’.
Infection
Ransomware is most commonly propagated through user-initiated actions, such as falling for phishing emails that contain malicious attachments or from users unknowingly visiting an infected website, in which case the malware is downloaded and installed without the user’s knowledge.
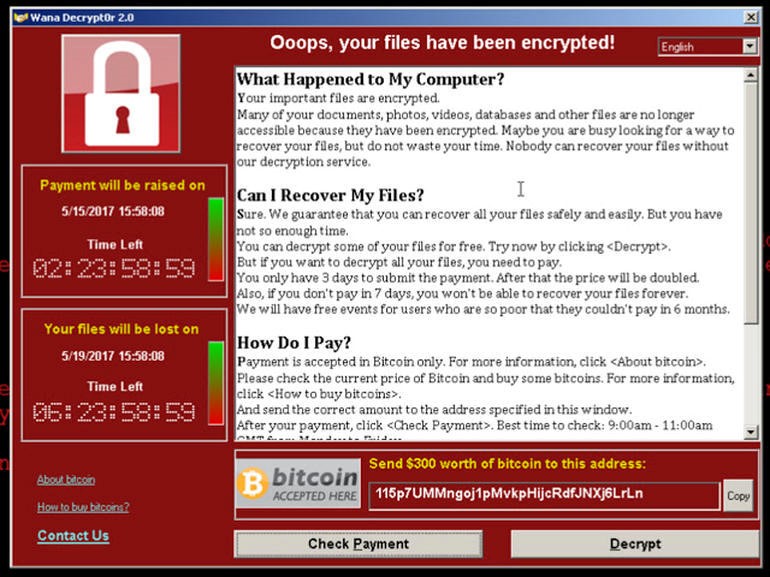
There are hundreds of ransomware variants, all of which work slightly differently. However, generally speaking, once the payload is executed on the target machine, one of the first actions taken is the encryption of the files on the hard drive. The virus then delivers a ransom note demanding payment in exchange for the decryption key of the victim’s files.
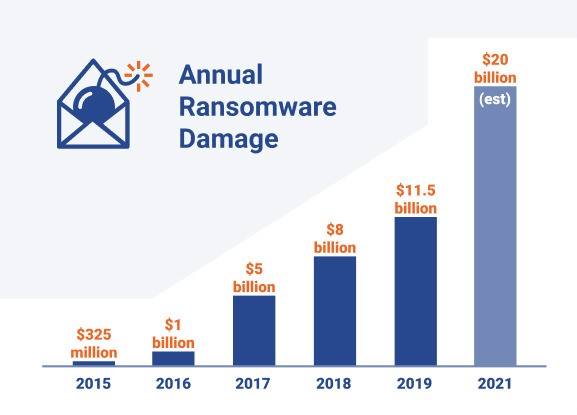
The annual damage caused by Ransomware continues to grow, as you can see in the chart below [5].
Below are a few more startling statistics regarding ransomware:
- Ransomware attacks have increased by 97% since 2017 – AttackIQ.
- 34% of those affected took a week if not more to restore full access, up from 29% in 2016 – Kaspersky.
- Ransomware generates over $25 million in revenue for hackers each year – Business Insider.
- A new business will fall victim to a ransomware attack every 14 seconds in 2019. In 2021, that number will be every 11 seconds – KnowBe4.
Prevention
As ever, when it comes to security there is no silver bullet. It is always recommended to provide as many layers of protection as possible, thus adhering to the ‘Defense-in-Depth’ principle. With that being said, there are many prevention and mitigation techniques that could (and should) be carried out to help defend against ransomware attacks. Below are some of the more obvious ones, and arguably some of the most important:
- User training – As mentioned above, one of the most common ways companies get infected with ransomware is due to user initiated actions. Therefore, user training seems like an obvious place to start when discussing prevention. Users should be taught how to spot suspicious emails, identify malicious links, and not open attachments contained in such emails.
- Spam filters – Don’t give users the chance to click on a malicious link! Implement an anti-spam solution to stop phishing emails from reaching the network. Consider adding a warning banner to all emails from external sources, reminding users of the risks. You can also utilize things like SPF, DKIM, and DMARC to improve email security.
- Antivirus – If the two steps above don’t work and malicious software makes its way onto the network, the next line of defense will be antivirus software. Companies should enable regular AV scans, ensuring antivirus software is enabled to automatically update signatures. Signatures of known ransomware variants are widely available online, so it might be worth running signatures from some of the more popular ransomware variants through VirusTotal just to make sure your AV provider will spot them.
- Internal Network Hardening – Beyond preventing initial access, the next best thing you can do to combat ransomware is to hinder its spread, by making lateral movement and privilege escalation on your network more difficult. We’ve discussed some common hardening tips in the past that are relevant here, but focusing on things like weak passwords (remember your service accounts too), the principle of least privilege for accounts, users not being local administrators of their own systems, not sharing a common local administrator password across systems, etc. This can be a long list, but these most common techniques are going to be what any attacker or piece of malware uses to further compromise your environment.
Mitigation
If the above steps fail to prevent a ransomware attack, there are several steps that can be taken to mitigate, contain, and recover from an attack that has occurred. Again, this isn’t an exhaustive list by any means.
- Immediately disconnect the infected system from the network to prevent infection propagation.
- Engage a third-party that specializes in incident response to help you deal with the issue and understand the initial infection point.
- Determine if a decryptor is available – There are many freely available ransomware decryptors online for some less sophisticated ransomware variants.
- Restore files from regularly maintained backups.
Conclusion
We hope this blog has given you a helpful introduction to ransomware, as well as demonstrating the serious threat it poses to organizations. As mentioned above, the prevention and mitigation measures listed are by no means an exhaustive list, but more of an idea of some of the measures that can be taken to defend against Ransomware attacks. If you believe your company may be vulnerable to Ransomware attacks, please feel free to contact us, and we’ll be more than happy to help.
References
[2] https://www.varonis.com/blog/a-brief-history-of-ransomware/
[3] https://coincenter.org/link/why-ransomware-criminals-use-bitcoin-and-why-that-could-be-their-undoing
[5] https://spinbackup.com/blog/24-biggest-ransomware-attacks-in-2019/