
What Penetration Test Reports Will I Receive Following An Assessment?
One of the key outcomes of a penetration test (or any type of security assessment) is the deliverables or reports. This is really what you’re paying for when you commission a third-party to perform an assessment, as this provides your view of what happened during a penetration test. From making sure that every finding in our Technical Findings Report is curated, meaningful, and actionable for your organization, to ensuring our Executive Summary Report is clear, concise, and easily consumed by members of your organization, we pride ourselves on producing high quality penetration test reports.
Many times, the penetration test reports are all someone sees of our work. And even though we like to present our findings and documentation to clients, the reports need to be able to stand on their own and showcase our assessment. Awesome reporting is just as important as doing a thorough and accurate penetration test. Here, we’ll cover our standard deliverable set for our penetration tests and most strategic security assessments, at a high level. If you’d like to know more, contact us to get our most recent set of sample reports.
Executive Summary Report
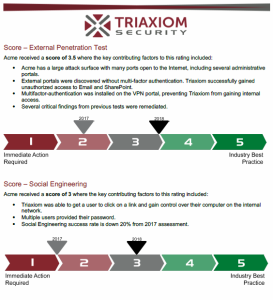
This report is meant for consumption by management and non-technical stakeholders. It’s a great way to present the findings from a security assessment or penetration test, without getting into all the gory technical details. This can be considered the 10,000 ft. view of your performance on an assessment. The Executive Summary Report summarizes the assessment, detailing the:
- Scope
- Types of testing performed
- Scoring that details how your organization performed compared to security best practice
- Strengths and effective security controls observed
- Critical or Thematic Security Issues
Technical Findings Report
The Technical Findings Report is a complete, detailed breakdown of every individual issue and vulnerability uncovered during the security assessment or penetration test. This report is intended for the IT team or security practitioners that are tasked with going out and remediating the identified issues. This report includes a bevy of technical details about each vulnerability, including:
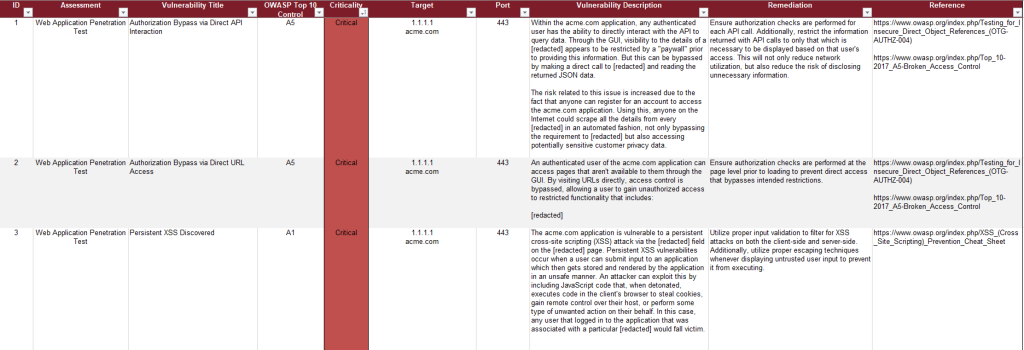
- Physical Site or Location (if applicable)
- Regulatory Requirement or Best Practice Standard (e.g. OWASP Top 10, PCI DSS)
- Severity/Priority
- Host/Port Affected
- Vulnerability Details, including how to recreate the issue and the associated risk
- Suggested Remediation
- Reference Links
Certification Letter

The third and final document is an optional item that you may want following the completion of a penetration test. A Certification Letter is meant to be a memo-style, one-pager that can be provided to your customers, clients, or third-parties in order to showcase that you’ve completed a penetration test, explain the scope of testing, and how your company performed. If the Executive Summary Report is the 10,000 ft. view of your company’s security performance, a Certification Letter should be considered the 50,000 ft. view. This document is a better fit for sharing with others because it doesn’t get into the technical details or highlight any specific shortcomings in your organization’s security posture, allowing you to avoid airing any dirty laundry. Many times, our clients will want something like this after going through the retesting process, once any vulnerabilities discovered during testing have been remediated/mitigated and subsequently validated. This document will highlight:
- What was in scope for testing
- What types of testing were performed
- How your organization performed (on a generic rating scale)
- What security strengths were observed
- Our contact information as references for the testing performed
Presentation of Findings
Following the completion of the project and the delivery of all penetration testing reports and documents, we always like to sit down (either virtually or physically onsite) to walk you through the documents we provide. We use this opportunity to:
- Orient you with the documentation
- Explain our findings
- Highlight some of the risks we think are important
- Discuss your organization’s path forward for remediation
- Answer any questions you may have
We feel presentations are really important and we try to make this meeting as interactive as possible. It allows us to highlight one of our core tenets of partnering with our clients.




