What’s the Difference Between a Penetration Test and Vuln Scan?
Knowing the difference between a penetration test and vulnerability scan is critical to optimizing your resources and making sure you are taking the necessary steps to reach compliance, secure your network, and determine your level of risk. Penetration tests are far more expensive and may be more than you need, while vulnerability scans, while cheap, might not be enough for your organization. Lets take a look at each and what the key differences are.
Vulnerability Scans
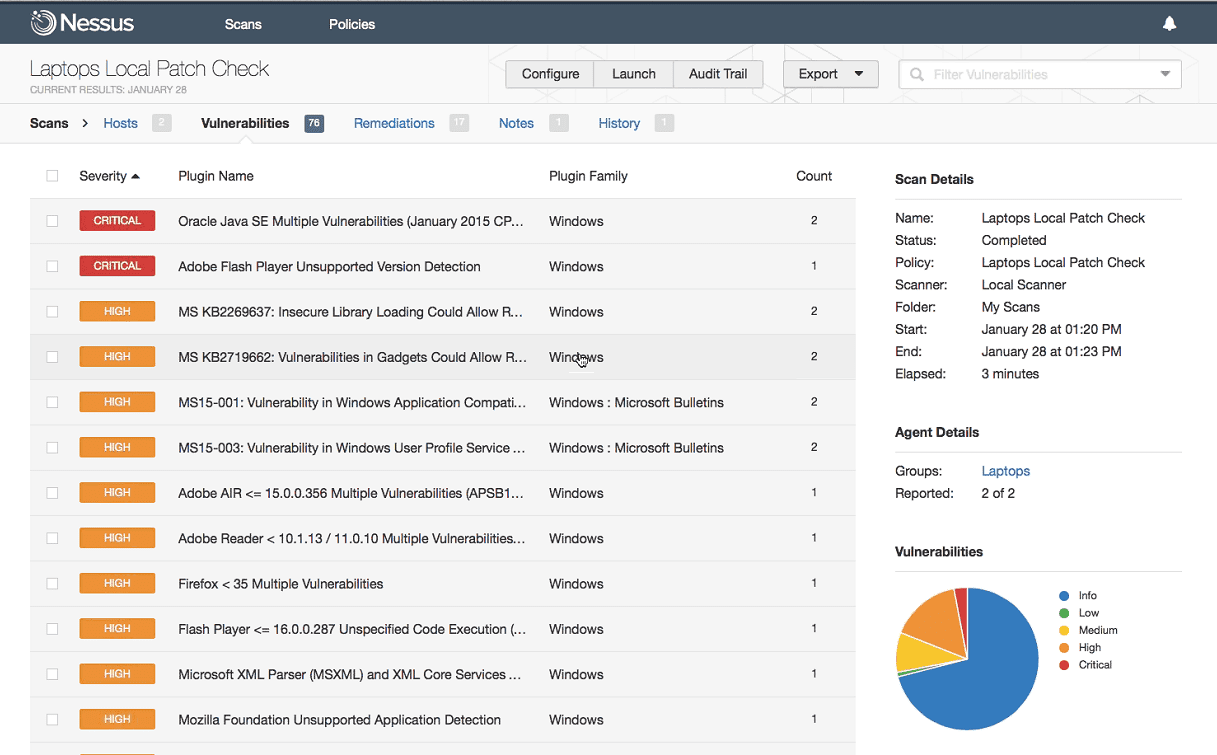
A vulnerability scan is an automated test using an off the shelf software. The scan will scan across you network for common vulnerabilities. Depending on how you have the device configured, this can be either an external or internal scan. The scanner will probe different systems and services across your network against a database of known vulnerabilities. If the scanner determines a system is vulnerable, it will report it and move on.
Vulnerability scans have two major advantages. First, they are cheap. Although there are some free scanners out there, a professional scan will cost you around $1,000 – $4,000 depending on the size of your network. Second, they are automated, meaning once it is configured correctly, you push start and wait for the results. Because of these reasons, many compliance standards require quarterly vulnerability scans. Quarterly vulnerability scans are an excellent way to ensure that your patch management process is working as expected, and that there isn’t a vulnerability that slips in that you are unaware of.
Penetration Tests
A penetration test by contrast is a highly skilled engineer, or ethical hacker, emulating an attacker trying to hack into your network. The engineer will abide by an agreed upon rules of engagement, which will list the scope of the engagement, the target objectives, and the rules he must follow to avoid problems. Similar to a vulnerability scan, penetration tests can be external and/or internal, but they can also meet a wide variety of subsets and be highly customized.
One interesting thing is that as part of a penetration test is that there will often be a vulnerability scan as part of the process. Unless the engineer is trying to be covert, she will use a vulnerability scan as part of enumerating the network. The penetration test will go much further than just a scan though. Once the engineer completes the scan, they will weed-out false positives by manually verifying the scan. A vulnerability scan will never exploit a vulnerability, leading to many false positives. Additionally, the engineer will demonstrate the risk of each of the vulnerabilities by actively exploiting the vulnerability, and trying to gain access to the network. A penetration test can demonstrate risk far better than a vulnerability scan because vulnerabilities are often combined and exploited in a chain, that demonstrates what an attacker may be able to achieve.
Penetration testing will also check for many things that a vulnerability scan will not. Most of this is due to the fact that it requires manual interaction, some base level of access to identify, or an overview of the network. As an example, one of the most critical findings discovered during an internal penetration test is a shared local administrator password. This is often set up for ease of administration. From a risk standpoint though, by sharing the same local administrator password across your network, an attacker who is able to compromise one of your systems (perhaps sally in accounting clicked on a link she shouldn’t have) that attacker now can access all systems in your network with that administrator password. It’s no wonder why that would be rated as a critical finding, and is often discovered during an internal penetration test. However, this will not be discovered during a typical vulnerability scan.
Summary
In summary, both vulnerability scans and penetration tests are an important part of a mature information security program. Vulnerability scans are cheaper and automated, meaning you can run them regularly without consuming resources. As a general guideline, vulnerability scans should be ran once a quarter, and after any major change to a system or the network. This will allow you to fix any issue that may have fallen through the cracks and ensure your patch management process is working as desired. Vulnerability scans, should not be used instead of penetration testing. Vulnerability scans do not adequately demonstrate risk, are often error prone, and will miss many vulnerabilities, some of which could have dire consequences. As such, penetration testing should be performed in conjunction with vulnerability scans. Most standards recommend penetration testing annually. If you’d like to discuss more, contact us.